Introduction to Ezrah Credentials (Part 1)

The Identity Revolution: Why Ezrah Matters.
Identity is broken. Not in theory, but in practice—every day. From signing up for new services to proving your qualifications, we constantly hand over sensitive data to systems we don’t control, hoping they keep it safe. But centralised identity models have failed us:
• Massive data breaches leak millions of personal records.
• Over-sharing forces you to reveal more than necessary—just to prove one small thing.
• Gatekeeping by big tech companies puts your identity in someone else’s hands.
Let's take a long down the historic line and get a proper understanding of how deep this issue goes.
Early days of identity systems
In the beginning identity verification was localised. In small communities, trust was established through face to dace interactions. No one needed a government-issued ID to prove they belonged. Things were simpler back then, fun times.
As society expanded, however, centralised systems of identity became necessary -- first in the form of paper documents, then in digital databases.
Governments and institutions began issuing identity credentials, like birth-certificates from hospitals, passports from immigration, social security numbers and a lot more. These systems worked and they worked effectively. But new problems emerged, born from the fundamental weakness of this system.
- They relied on centralised authorities. If an entity lost or misused data, individuals had little recourse.
- Our data and credential needs had extended beyond people, we now needed to offer credentials for objects, items, and even concepts (patents, tokens, receipts, and many more).
- The centralised services were slow and prone to mishaps and usage timeout, Every credentials that needs verification needed contact with the issuer to verify, and this introduce a large flaw, the allowance of forgery, and inconsistent systems.
The Digital Identity Era & Its Challenges
With the rise of the internet new ways to manage identity were introduce, but these too presented new problems. Traditional digital identity models—such as usernames and passwords, social logins (Google, Facebook, etc.), and centralised databases—became standard. These models solved some issues but created others:
- Data Breaches – Centralised databases became honeypots for hackers. When major corporations or governments suffered breaches, millions of identities were exposed.
- Lack of User Control – Users had little ownership over their digital identity. Their credentials were stored and managed by third-party companies, leading to concerns about data misuse.
- Fragmentation – Each service provider had its own identity system, forcing users to create multiple accounts across platforms, leading to a cumbersome experience.
So What solutions did we tried, 🤔
Attempts to Fix the System: Federated & Single Sign-On (SSO) Models
As identity problems became more apparent, new solutions emerged. Federated identity models, such as OAuth (used by Google, Facebook, etc.), allowed users to sign in across different platforms with a single login. This reduced friction but created a new problem: corporate gatekeeping. A handful of tech giants became the de facto identity providers, giving them immense control over online identities. While these solutions improved usability, they failed to address the core issue: true ownership of identity. Users still depended on centralised entities to validate and store their credentials. If Google or Facebook revoked access, a user could lose their digital identity overnight.
Another issue mentioned earlier is extensibility, We now have credential needs that extends far beyond just sign-on and single proofs, we have needs to present authorisations and credentials between each other far beyond the perimeters of one platform or the other.
So what options do we have, Well there is a new approach to this, one that leverages the advent of the blockchain. it's called Decentralised Identity.
Enter Self-sovereign identity (SSI): Owning Your Credentials.
The flaws in traditional identity systems—data breaches, lack of user control, and corporate gatekeeping—paved the way for a paradigm shift: Self-Sovereign Identity (SSI). SSI is built on the principle that individuals should own and control their identity without relying on centralised authorities.
What is Self-sovereign identity?
Self-Sovereign Identity (SSI) is a decentralised approach to identity management where users control their own credentials and decide who can access them. Unlike traditional identity models, where governments, corporations, or third parties act as gatekeepers, SSI empowers individuals with verifiable, portable, and privacy-preserving credentials.
At its core, SSI consists of:
- Decentralised Identifiers (DIDs) – Unique, self-owned digital identifiers that aren’t tied to any central authority.
- Verifiable Credentials (VCs) – Digitally signed attestations that verify an individual’s identity, education, or employment.
- Blockchain for Trust Anchoring – Instead of storing personal data on-chain, blockchain acts as a tamper-proof ledger that records the validity of credentials.
How SSI Fixes Traditional Identity Problems
SSI aims to solve the problems of centralised identity systems in three key ways:
1. User Ownership & Control
With SSI, individuals create and manage their own digital identity. Instead of relying on corporations like Google or governments to issue credentials, users store them in a digital wallet. They decide when, how, and with whom to share their data.
2. Enhanced Privacy & Selective Disclosure
Traditional identity systems often require users to overshare information. For example, proving your age at a bar requires showing a government ID, which also reveals your name, address, and more. SSI introduces Zero-Knowledge Proofs (ZKPs) and Selective Disclosure, allowing users to prove specific claims (e.g., “I’m over 18”) without exposing unnecessary details.
3. Elimination of Passwords & Reduced Fraud
Since SSI credentials are cryptographically signed and verified through decentralised networks, they significantly reduce phishing and identity theft risks. Users don’t need to create multiple passwords for different services—authentication happens using cryptographic proofs, reducing attack vectors.
Under the Hood: How Ezrah Works
Verifiable Credentials 101: What they are and why they matter.
Verifiable Credential (VC) is a digitally signed proof of identity, qualifications, or attributes that can be verified instantly without relying on centralised databases. Think of it as a digital version of your ID or diploma—but instead of being stored on a government database, it is issued directly to you and can be verified anywhere, anytime.
VCs consist of three main components:
- Issuer – The entity that issues the credential (e.g., a government, university, or employer).
- Holder – The individual or organization that owns and stores the credential.
- Verifier – Any party that needs to verify the authenticity of the credential.
How Verifiable Credentials Work
- Issuance – An organization (e.g., a government or university) issues a digitally signed credential and sends it to the user’s digital wallet.
- Storage – The user stores the credential securely in their own wallet, which could be on a mobile device or cloud-based storage.
- Verification – When needed, the user presents the credential to a verifier. The verifier checks the digital signature against a decentralised ledger to confirm authenticity without needing to contact the issuer.
At the foundation of Ezrah’s credentialing system lies the Decentralised Identifier (DID) — a new type of globally unique identifier that does not require a centralised registry or authority to issue or control.
Why Verifiable Credentials Matter
1. Instant & Tamper-Proof Verification
Unlike traditional credentials, which require manual verification (e.g., calling a university to check a diploma), VCs use cryptographic signatures that can be verified in seconds and cannot be altered or forged.
2. User-Controlled & Privacy-Preserving
Users own and control their credentials, deciding when and with whom to share them. Technologies like Zero-Knowledge Proofs (ZKPs) allow users to prove something (e.g., “I’m over 18”) without revealing unnecessary details (e.g., date of birth).
3. Reduces Fraud & Identity Theft
Since VCs are cryptographically secured and can be verified without a central database, they significantly reduce risks associated with data breaches, document forgery, and phishing attacks.
4. Cross-Platform & Global Adoption
VCs are not tied to a single organization or platform. They work across different industries—government, finance, healthcare, and education—making identity interoperable and universally verifiable.
What are DIDs
A DID is like a digital passport number that you own, one that’s cryptographically verifiable and portable across platforms, apps, and networks.
Key Properties of DIDs:
• Self-owned: Created and controlled by the user, not issued by a central authority.
• Cryptographically Verifiable: DIDs are backed by public-private key pairs and associated verification methods.
• Globally Resolvable: Using a DID resolver, anyone can fetch the corresponding DID Document to verify a signature or interact with a credential.
DIDs shift control of identity back to the individual. They enable:
• Credential portability: Use the same DID across services.
• Decentralised login: No passwords; authenticate with cryptographic proofs.
• Interoperability: DIDs work across blockchain ecosystems, apps, and regulatory frameworks.
With Ezrah, DIDs are not just identifiers — they’re access keys to a new trust layer on the internet.
Plugging In: Tools for Developers and Businesses
Ezrah Dashboard
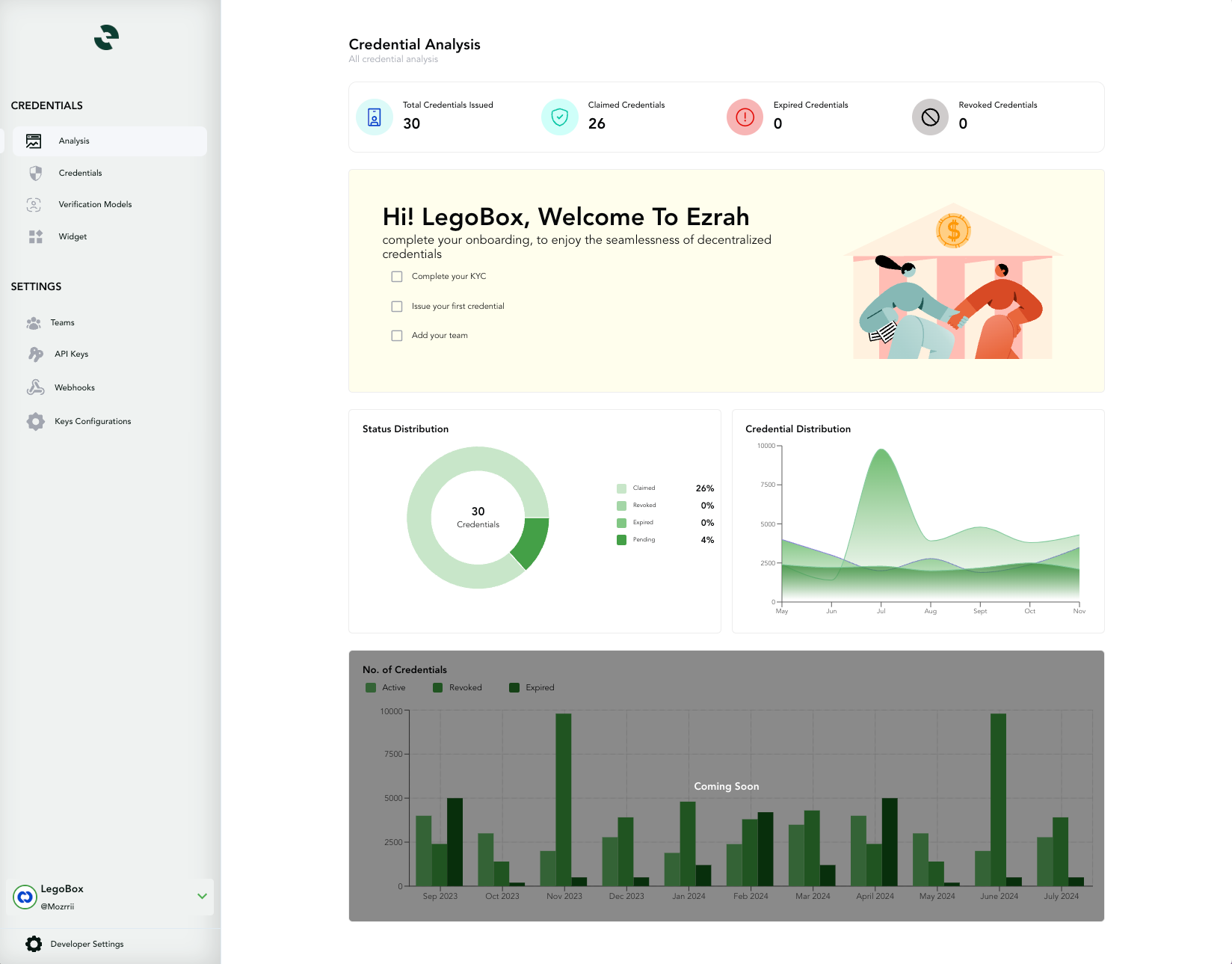
• Issue, revoke, and manage credentials
• Track credential verification events
• Add branding and configure credential schemas
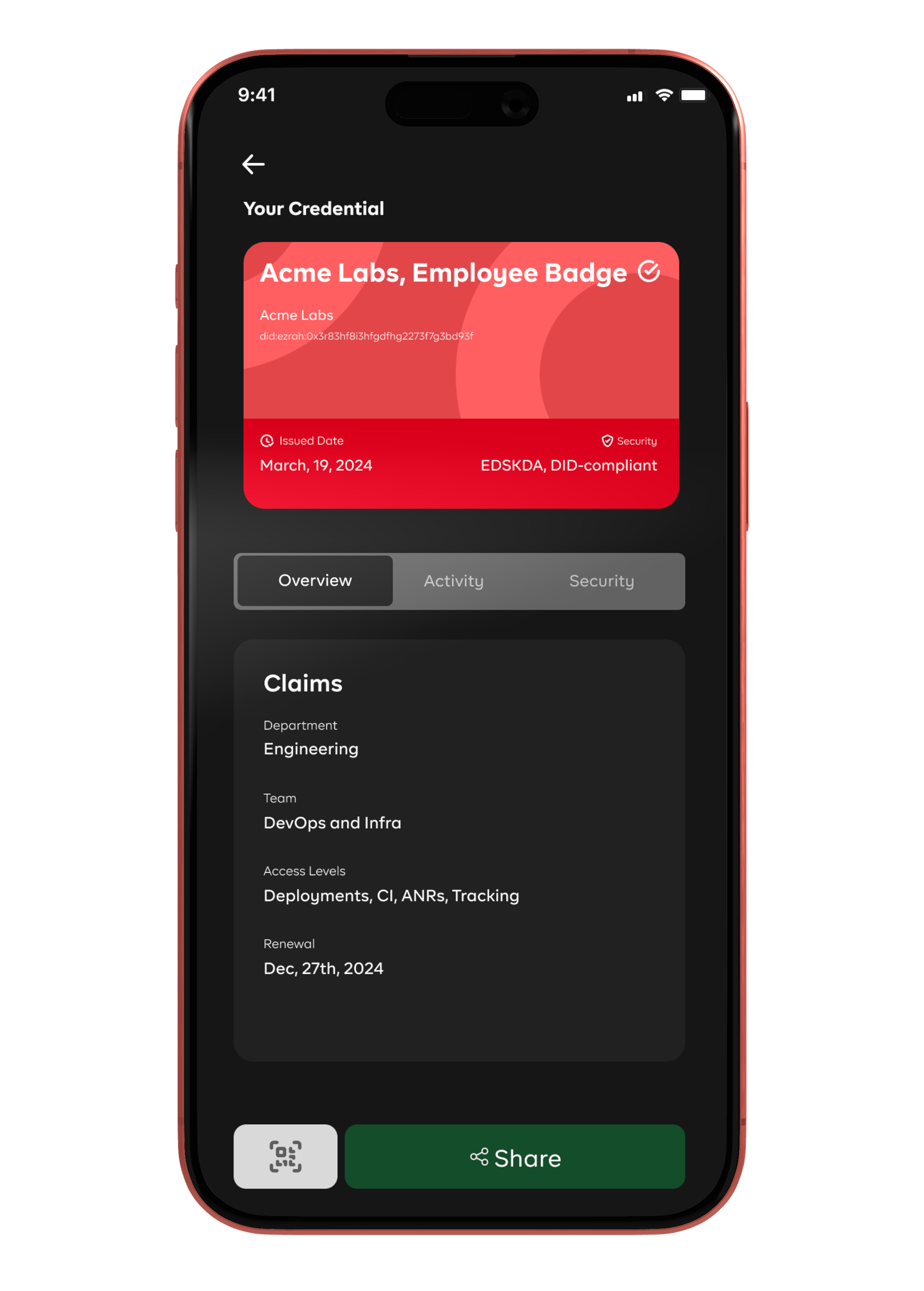
Ezrah Wallet (Mobile App)
• View and store all verifiable credentials
• Respond to verification requests via QR or deep link
• Supports biometric protection and passcode
Whitelabel Solutions
Need something branded for your organization? We offer:
• Custom mobile wallets
• Hosted credential vaults
• SDKs and widgets for web/app credential workflows🔌 Plugging In: Tools for Developers and Businesses
Conclusion.
As we’ve explored, Verifiable Credentials (VCs) and Decentralised Identifiers (DIDs) are reshaping how identity works in the digital world. Instead of relying on centralised databases, fragile paperwork, or trust-by-association models, we now have the tools to create cryptographically verifiable, privacy-preserving, and interoperable credentials.
This shift isn’t just technical—it’s philosophical. It places control back in the hands of individuals while giving organisations a more secure, scalable, and trustworthy way to issue and verify claims. Whether you're verifying age, education, financial status, or employment history, the process becomes faster, safer, and less reliant on third-party intermediaries.
From governments and enterprises to developers and end-users, the applications are broad—and the implications are profound. We’re moving toward a world where trust is no longer a static asset held by institutions, but a dynamic interaction underpinned by cryptography, transparency, and user consent.
The infrastructure is here. The standards are maturing. What comes next is implementation—at scale.